By Brian Prentice and Paul Mee
This article first appeared in Forbes on April 11, 2018
In March, the U.S. Department of Homeland Security and the Federal Bureau of Investigation issued a troubling alert: Since the same month two years before, Russian state-sponsored hackers had been infiltrating the nation’s electricity grid and various infrastructure industries, including aviation, collecting information on how the networks were organized and what systems’ controls they had in place. While no sabotage appears to have been perpetrated, the unsettling question remains – what were they going to do with the data they collected?
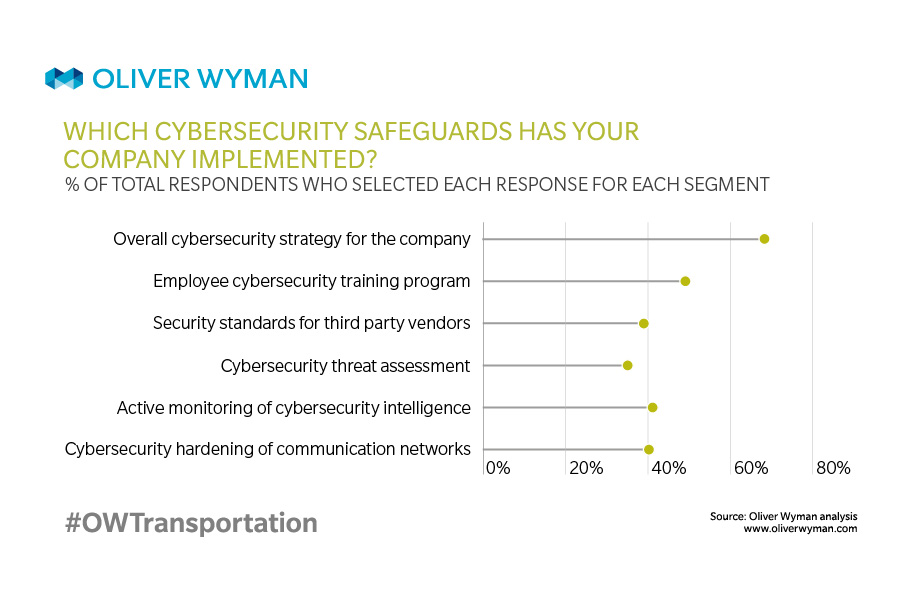
While all these industries, especially their biggest players, tend to have extensive cybersecurity in place, it may not be as comprehensive as the nation would hope. Instead of gaining access through the front door, where the alarm system was more robust, these hackers simply went around back and entered through the more vulnerable networks of third-party and supplier operations, relying on myriad techniques including the use of phishing emails infected with malware and the theft of credentials.
Needless to say, the scenario should send chills throughout the aviation industry. While major aircraft manufacturers and airlines make obvious targets because of the potential they represent to conspicuously disrupt international commerce, they also rank high on hackers’ to-do lists because they maintain global, highly interconnected supply chains that over the past few years have been aggressively digitizing operations. More digitization means more attack surface for hackers. The many links on aviation’s supply chain – some big, many small to midsize – all become potential vulnerabilities for aerospace giants, given the daunting task of ensuring that all vendors with access insist on the same level of rigor in both their cybersecurity and their employee training.
Vulnerabilities in the supply chain
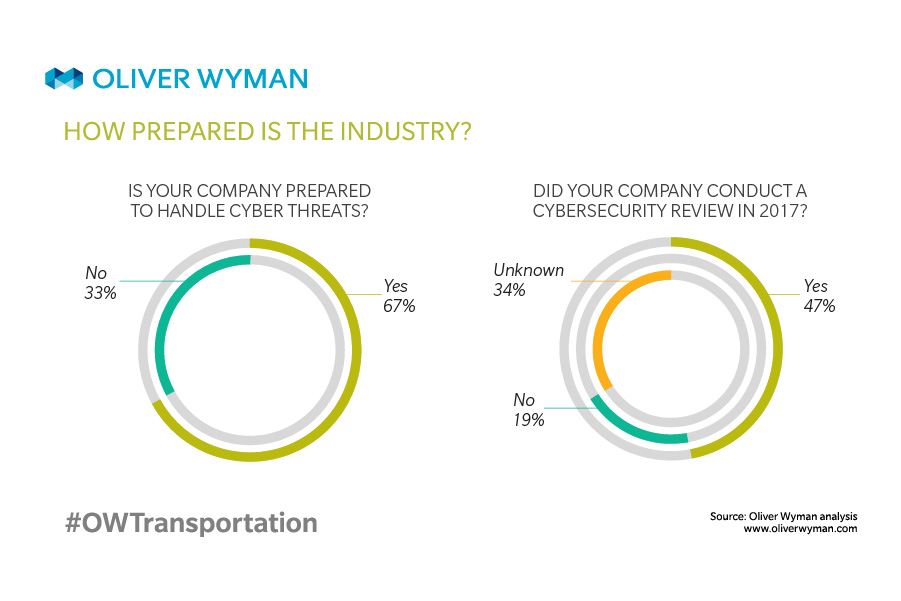
The biggest organizations within the industry’s fold may have advanced cybersecurity; the same cannot always be said about the vast network of service providers and suppliers, many of which are members of the maintenance, repair, and overhaul (MRO) industry that services the nation’s aircraft.
To read the rest of the article, please click here.